|
Sangeetha Sridhar Articles |
Other useful Articles

Who said
technology is just for geeks? For all the rest of us who love having some
fun, there is so much of humour in technical jargon that sometimes crosses the
thin-line to be even called weird. This week under Digital Oman, let’s get
light-hearted with the mood of the good weather and have fun knowing some
technical jargon that we have confronted and mastered.
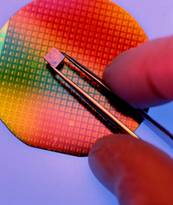
The
fundamental favourite potato chips have been adapted into technology terminology
for the basic unit of processing element in computers. Compressed silicone
cylinders are slices it to thin wafers, and etched with intricate circuitry to
work as the fundamental technical component that processes all inputs fed into
computers. A set of such ‘chips’ are combined to form the elaborate
integrated circuit-board or the IC, hence the name IC Chip. You can now ‘boot’
(kick) not just people if warranted but also computers, meaning you power it on
and start loading the operating system software.
There are
several terms that have been used casually, encoded by the software sector which
has stayed on to mean entirely different things in the context of technology.
For example a ‘Window’ was something that gives us a glimpse of the outer
world from inside your office or home. But today it signifies the technology
industry’s leading product developed by the Microsoft. Windows consists of a
desktop client and server versions of software which bundle several utility and
productivity tools as a suite.
The age old
A is for ‘Apple’ - the fruit, and now it’s for Apple - a company that has
made several products including laptops, desktop computers and the adorable
iPhones under this single famous name with elegance and style which come at a
special price. A ‘cell’ as a biological unit of living organism is now
the ‘box’ where a column and a row intersect, in a spreadsheet. Again ‘memory’
is made up of chips that temporarily hold data or instructions in a computer.
A ‘Zombie’ which sounds
almost like an African tribe is technically speaking, a computer that has been
taken over by hacker and using special software he/she can remotely use the
computer even for malicious purposes. The infecting software creates a ‘back-door’
(not the door at the back of a building) for the hacker who then injects
malicious software through this open door, right into a zombie computer.
Currently millions of home / office computers have been turned into zombies by
powerful hackers. Famous websites like the Yahoo and the Amazon were once taken
down by data or instruction floods sent from such a network of zombie computers.
Even the
youngest child we come across would recognise the ‘Mickey’ as the mouse
is Disney’s cartoon series and he is the funniest mouse on earth. Most of us who
know that a ‘mouse’ could also be the small input device we work with to
operate our computer, wouldn’t know the fact that a unit of our mouse movement
in called a Mickey.
Honey pot
is something we normally dig-in to add a dash of honey to our favourite
breakfast cereals. But in the weird world of technology a ‘honeypot’ is a
decoy computer, (with seemingly important files) in a network that is connected
to the Internet to allure hackers. Such honeypots play an important role in
enhancing the security within a computer network, by giving a better
understanding of how malware and hackers leech on to potentially useful files by
gaining access through unlawful means.
A blob in
the common world meant a giant drop of any odd liquid or gooey flesh, but in the
world of technology it has a completely different meaning. A ‘blob’ is a
binary large object which is a sizeable chunk of binary data collected and
stored as a single entity in a database management system.
A mash-up
is a food delicacy prepared with boiled potatoes, butter and cream. But in the
world of software applications, a mash-up is a new breed

of web-based applications
that combines two entirely different web-services to create a new, potentially
more useful service for users. For example, a ‘mash-up’ of Google maps
and weather data can give a realistic image forecast of current weather of a
given location. To make it more useful, a geo-sensitive mobile devices that can
connect to the Internet can be set with the ‘push’ technology (Yes ‘push’
as in push data) to receive live weather alerts.
Anyone
heard of the ‘id10t’ error? Few of us in the technology world know that this is
a code name for errors caused by an in-experienced user (or simply ‘idiot’)
who doesn’t know that he is actually the cause of the error. Such terms are
normally coined at technical support environments which later spread to wider
use.
Squat is
simply a very good exercise prescribed to strengthen one’s thigh and calf
muscles. But in the cyber world a ‘Cyber-Squat’ is a legal offense where
by a user register a website name of a famous person or an organisation first
and then negotiates a price for giving it away to the rightful person.
The
innocent looking abbreviation ‘SLP’ normally used in SMS or chat messages
to indicate ‘sleep’, morphs in the world of technology into a complex
communication protocol called the ‘Service Location Protocol’.
A packet is
what we know to cover products and make it more attractive and safe enough to be
transported. But in technical terms any data traffic in a network is split into
uniform sized chunks with its own header and trailers labels and each of these
chunks is termed a ‘packet’. Even the Internet routes a set of such
packets randomly to its destination where they are correctly assembled and
decoded into a coherent message.

A sparc may sound like a
unit of fire, but it is indeed the name of a processor series that was developed
by the SUN Microsystems, based on a ‘Scalable Processor Architecture’ model. A ‘web’
is not only that which is spun by spiders but it is also the mesh of computers
that span the globe, exchanging information and enabling communications. The
adventure of riding a wave, in the Internet parlance means ‘surf’ or
browse the Internet.
A ‘bridge’
is built normally over a water-body to enable traffic across and interestingly
in network terminology, a bridge is device which connects multiple network
segments at the innermost data layers. ‘Overflow’ doesn’t happen only in
the case of liquids but it can also happen when there is no longer enough memory
to hold the data that is sent in.
A’ tag’
that normally labels instructions or the price of items has also entered the
world to technology. It is now used by web-developers to created itemised
contents for the web-pages with relevant key-words that help search engines like
Google or Bing to bring out the relevant pages when these key-words are searched
for.
‘Triggers’
are not just found in guns but they are also liberally found in software modules
that fire off or activate other pieces of code when certain programmed condition
occur. Even when code errors occur programmed triggers spark off generating
error codes.
One would
normally expect a handle, to mean the ones encountered in a vessel of a door or
a piece of equipment. In technical jargon, a ‘handle’ is a screen name
used in online chat rooms or other social media so as to protect one’s identity
and yet give a unique name. Usually hackers are known to have creative handles
such as ‘darkWater’, ‘LockerGnome’, ‘rootSucker’, etc.
RAM
and DOS which could be normally be names of people in a particular
community, double up as ‘Random Access Memory’ and ‘Disk Operating System’ in
the digital realms. Biological virus cause illness to living beings, while rogue
software ‘virus’ infect and take down even powerful computers that are
not adequately protected. Similarly a ‘bug’ is an insect in the real
world while it means an error in software programming parlance or a technical
flaw in a hardware solution.
‘Twitter’
– a sound that birds make is now a social networking website and a conference
among this community of members is called a ‘chirp’ - another bird call.
The scary ‘trolls’ online are infamous online chat users who introduce
disturbing links, mimic other users’ posts and profiles even engage on verbal
wars with others online members.
As time
moves on we come across new terms and old words with new meanings and learn to
adapt to their new meaning by repeated use. It only takes a good weather day to
sit back relaxed and think retrospectively as to how these common words once
meant something so simple in our lives, have been very much complicated by
technology. Until we meet again, boot your windows, run your mouse and keep
surfing the web.
The
author is a technology evangelist working as Consultant at the Information
Technology Authority of Oman and can be contacted at
sendsangita@gmail.com or through her blog at
http://digitaloman.blogspot.com or on twitter at
http://twitter.com/sangitasridhar .
|